Context Conversations preview: Medsec with Jacki Monson and Josh Corman
Earlier this month at the Black Hat cybersecurity conference in Las Vegas, two cybersecurity researchers presented work showing how a hacker could deliver a potentially lethal shock through a Medtronic pacemaker by exploiting a vulnerability in its software.
As Jonathan Butts, CEO of QED Secure Solutions, and Billy Rios, founder of WhiteScope, publicly debuted their research demonstrating that firmware updates to the devices are unprotected by even the most basic encryption standards, they said they had first notified the pacemaker manufacturer in January 2017—more than 550 days prior. Medtronic, they said, had responded with a combination of crickets and dismissals.
“They could have fixed this for $20,000. Their competitors have fixed it,” Butts told The Parallax. “Even the director of the FDA tweeted support for us.”
#FDA is appreciative of our work and collaboration with the white hat hacker community, and their help in identifying vulnerabilities. Improving MedTech cybersecurity requires this open dialogue. We’re advancing new efforts to achieve cybersecurity goals. #BlackHat2018 @XSAniper
— Scott Gottlieb, M.D. (@SGottliebFDA) August 9, 2018
The incident is demonstrative of the rocky road medical-security professionals are attempting to navigate: not just flawed software, but also a lack of willingness from vendors and users alike to acknowledge that it’s flawed—let alone in need of repair.
Medical-security professionals must also contend with ransomware, as well as destructive computer worms like WannaCry. The threat of deaths or injuries resulting from unpatched cybersecurity flaws seriously concern everyone involved—technology vendors, doctors, patients, administrators—but as technology advancements enable more effective and efficient healing, or longer-lasting health, medsec hackers’ warnings don’t seem to be resonating.
Does the cure for sick software lie in vulnerability disclosure regulation? Better backups? Or some panacea waiting to be invented?
READ MORE ON MEDICAL SECURITY
Biohacker’s latest answer to health care hurdles: Homebrew meds
On doctors’ orders, Israel plans a health care CERT
WannaCry vs. the ER doc: On the front lines of a ransomware outbreak
Yes, your life-saving medical devices can be hacked
Critical systems at heart of WannaCry’s impact
Time for a Department of the Internet of Things?
Hackers call for federal funding, software security regulations
The edge of heartbreak: Researcher hacks her own pacemaker
In the interest of exploring these questions and more with the cybersecurity and hacker communities and beyond, Javelin Strategy and Research, New Context, Rain Capital, and The Parallax are proud to announce the first Context Conversations speaker series, following last year’s Enigma Interviews.
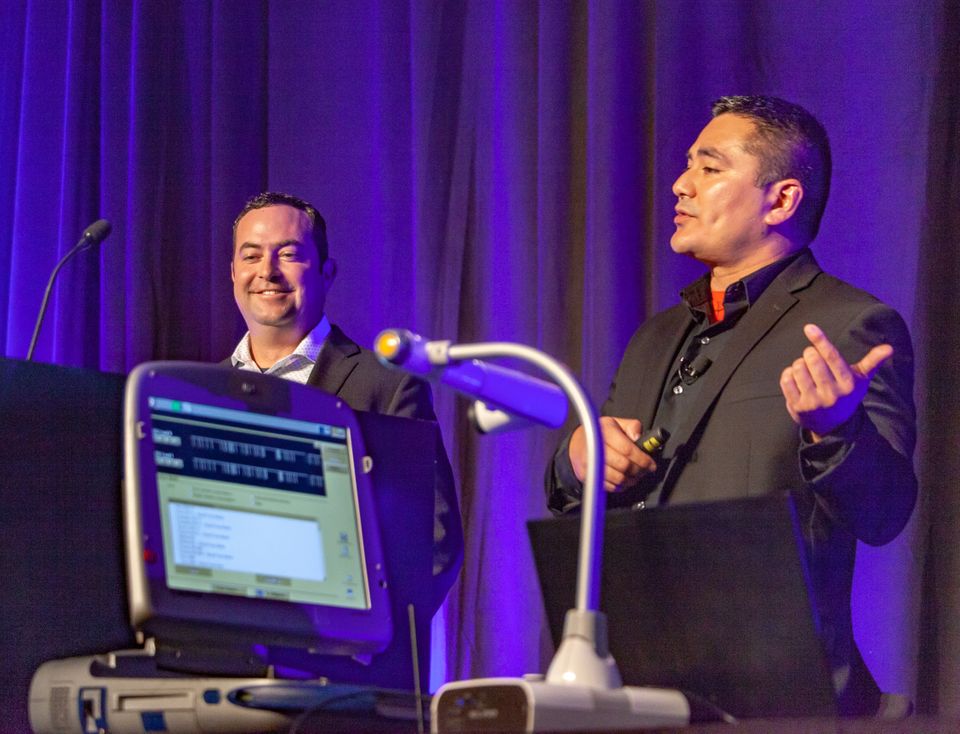
At 7 p.m. PST on Thursday, September 20, at the Digital Garage in San Francisco, I’ll moderate an on-stage conversation between Jacki Monson, chief privacy and information security officer of Sutter Health, and Josh Corman, chief security officer of software maker PTC. We’ll discuss a few of the most complicated yet critical issues health organizations face in securing their systems and thus keeping their patients safe.

Monson has worked in health care for 16 years. She holds certifications in health care law, privacy, information security, and compliance. As a member of the National Committee on Vital and Health Statistics, she frequently speaks at events about the subjects.
Before joining Sutter Health, Monson served in privacy and security management roles at health care and pharmaceutical providers, including Mayo Clinic. And as a member of the U.S. Department of Health and Human Services’ Health Care Industry Cybersecurity Task Force, she has testified before government and legislative committees. She holds law and bachelor degrees, respectively, from the Mitchell Hamline School of Law and the College of Saint Scholastica.
Corman is co-founder of I am The Cavalry, a volunteer technology security organization. He also serves as an adjunct faculty member of Carnegie Mellon University’s Heinz College of Information Systems and Public Policy, as well as a member of the Congressional Health Care Industry Cybersecurity Task Force. He previously served as director of the Cyber Statecraft Initiative for the Atlantic Council, chief technology officer for Sonatype, and director of security intelligence for Akamai.
Corman is passionate about encouraging better security responses to threats facing our increasingly vital digital infrastructure. His approach to security in the context of human factors, adversary motivations, and social impacts has helped position him as one of the most trusted names in security.
In addition to moderating Corman and Monson’s discussion, I’ll be asking questions from the live audience and people watching the live stream. You can sign up to attend the free event in person here. If you’re unable to join us, we will be live-streaming the conversation here.
You can start submitting questions to The Parallax on Twitter or on Facebook, or Context Conversations on Twitter, using the hashtag #ContextConvo. Thank you!
