Your next flight itinerary could be easily hacked

HAMBURG, Germany—The last thing you should ever do with an airplane boarding pass is post a photo of it online.
In doing so, you could be handing your personal information to hackers, says Karsten Nohl, the CEO and founder of Berlin-based Security Research Labs. He demonstrated here late on Tuesday evening a live hack at the 33rd annual Chaos Communication Congress, the largest European computer security conference, that with nothing more than a boarding pass bar code, a hacker could steal your airline miles, gain access to your personal information, cancel flights, stalk you while you travel, and even change your ticket so that your next flight is registered to him, not you.
The problem exists on all boarding passes across the airline industry, Nohl tells The Parallax.
“No matter where you book your flights, no matter what airline you fly, they all share similar issues,” he says. “There’s no access control, no way to authenticate travelers, and no logging to track abuse.”
Multiple airlines contacted for this story—including Lufthansa and Air Berlin, which Nohl used in his demonstration—did not respond to requests for comment. Air Berlin forwarded the request to the German Aviation Association.
Claudia Nehring, a representative for the airline industry organization, said in a German statement translated to English, “The systems have a multilayered mechanism to defend against ‘brute force’ attacks and other automated attacks. This should prevent excessive requests from single systems. In addition, account activity is monitored by an automated system, as well as by human operators.”
Air Berlin also requested on Twitter that a tweet about Nohl’s live-hack demo by a conference attendee be removed for calling attention to the research. That request was apparently honored, as the original tweet has been deleted. The Parallax was able to get a screenshot of the original tweet.
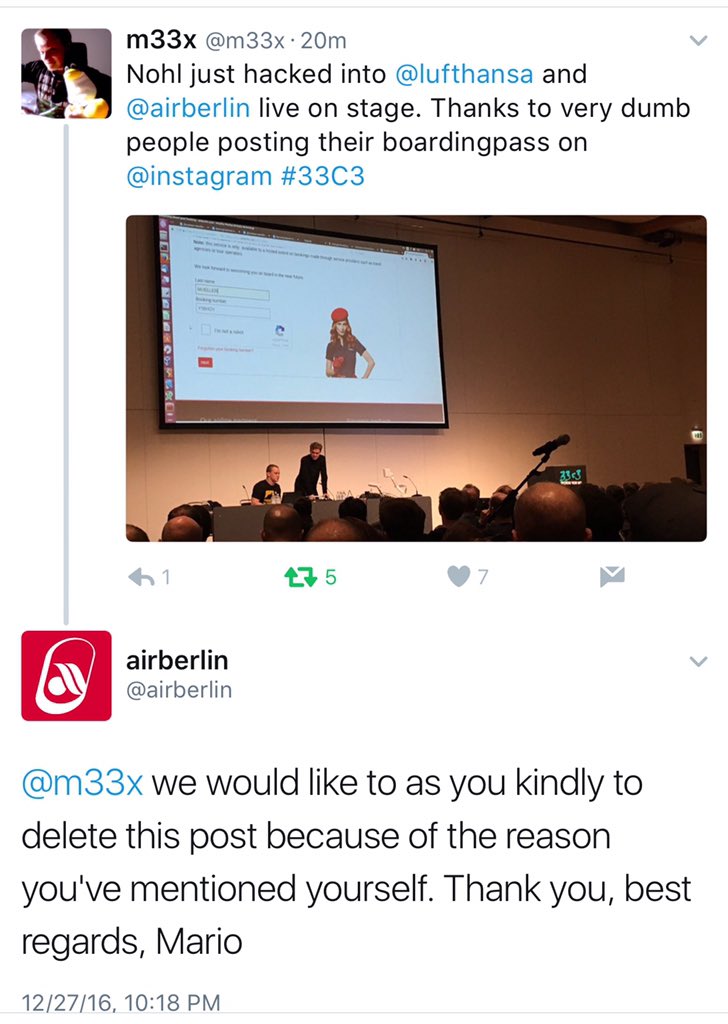
Screenshot of a tweet that Air Berlin asked to be deleted because it highlighted vulnerability research in airline boarding passes demonstrated at the 33rd annual Chaos Communication Congress in Hamburg, Germany. Reader-submitted screenshot to The Parallax
Nohl and his partner on the project, Nemanja Nikodijevic, says that because the problem is “industrywide,” he did not reach out to airlines before demonstrating the hack, a commonly accepted practice in the computer security research community.
“Nobody seems to be a responsible disclosure partner for this,” he says.
Research by Nohl and Nikodijevic into the Global Distribution System travel-booking network infrastructure found that it doesn’t have much in the way of even a basic modern security protocol, making boarding passes extremely susceptible to exploitation.
While there are about 20 GDS vendors at the moment, Nohl and Nikodijevic investigated three major ones: Amadeus, Galileo, and Sabre. A hacker armed with another person’s boarding pass bar code can wreak havoc for travelers, putting valuable personal and financial information—not to mention travel plans and even physical safety—at risk.
Nohl partnered with a German television station to show how anybody who flies is at risk. Nohl and the station, ARD, were able to find out which flight a German politician was on, and purchase an empty seat next to him for a reporter.
Nohl told his audience Tuesday night that the motivating question driving the research was, Do GDS networks “have normal, basic security?” He concludes that they don’t.
GDS networks store travellers’ names, email addresses, home and work phone numbers, credit card numbers, home addresses, frequent-flier numbers, and timestamped records of Internet addresses from which tickets are purchased. This mission-critical personal information, which security experts advise people to protect behind closely guarded, complex passwords and two-factor authentication, are protected in GDS networks by six-character codes made of letters and numbers, Nohl says.
“There are no passwords involved. The only authenticator [are these] six-digit sequences that people post on Instagram, print on their boarding passes, and that [hackers] can brute-force on their websites,” he says.
READ MORE ON TRAVEL AND SECURITY
How to protect your data when traveling internationally
How to securely send your personal information
How to protect yourself when using airplane Wi-Fi
Most, if not all, airline websites do not use commonplace security technology to prevent such attacks, which are nothing more than computer-driven attempts to guess the six-character codes by running through thousands of six-character codes at a time.
These codes use a character set taken from computer punch cards. To avoid confusion with the letters L and O, they avoid the numbers 1 or 0, and they can’t support nonalphanumeric symbols such as ampersands, exclamation points, or “at” signs, either. ”All ancient stuff,” Nohl says. Hackers can generate multiple accurate results in as little as 10 minutes.
Putting fliers’ information even more at risk is that this data is no better protected inside the GDS companies, Nohl says. “People working at the GDS companies have access to everything, including their support staff.”
Nohl and Nikodijevic aren’t the first to research boarding-pass security, but their work demonstrates a level of insecurity not previously realized.
An employee of a GDS company based in Europe spoke with The Parallax on condition of anonymity. With more than 10 years at the same company, he acknowledges that Nohl’s research reveals a problem but overstates its severity.
The frequency of boarding-pass bar code hacking “has to be utterly tiny,” he says. “Otherwise, we’d hear something about it. For all sorts of abuse, we have bigger abuse of the system from travel agents who are trying to screw airlines.”
Besides locking down website security to prevent brute-force attacks, which is high on Nohl’s list of remedies for the problem, the GDS employee says consumers shouldn’t expect changes anytime soon.
“The travel industry is not just one gigantic app,” he says. “The pain here isn’t building the software; it’s changing the market,” as well as changing government regulations.
“Every airline that flies to Europe has an obligation to follow European regulation,” he says, adding that it would take nothing short of government regulation “to change the booking systems in the background to be more privacy-aware. It’s just a question of generating momentum.”
