How to protect your data when traveling internationally
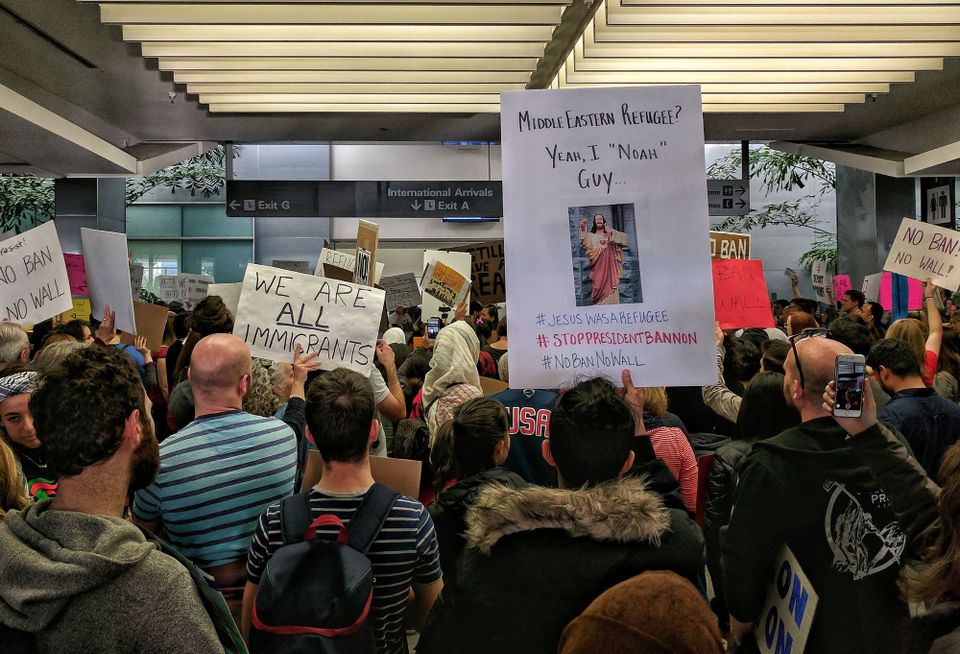
When U.S. Customs and Border Protection agents implemented President Donald Trump’s unprecedented executive order on immigration and refugees on January 27, they subjected more than just visitors to the United States to a tougher level of scrutiny before allowing them to enter the country.
Before U.S. District Judge James Robart halted the president’s chaos-inducing order, CBP agents revoked the green cards of nearly 60,000 noncitizen permanent residents and demanded that U.S. citizens re-entering the country, among others, unlock their phones, laptops, cloud storage, and social-media accounts.
Although scrutiny of travelers’ electronic devices and social-media activity is nothing new, the scope of it is, says Fred Jennings, a digital-rights attorney at New York City law firm Tor Ekeland.
READ MORE ON TRAVEL AND SECURITY
Your next flight itinerary could be easily hacked
How to securely send your personal information
How to protect yourself when using airplane Wi-Fi
New Zealand defends its border device search policy (Q&A)
“A year ago, there were some stories that this might become a policy,” says Jennings, referring to systemic social-media account searches at airports and other border checkpoints. House Republican Vern Buchanan proposed legislation supporting such searches in 2015.
Through research he has conducted to track people affected by the immigration order, Jennings says CBP agents have searched devices of a number of green-card holders and travelers with U.S. citizenship, in some cases also demanding that they hand over passwords to their devices and accounts.
“In pretty much all cases,” Jennings says, CBP officers have searched travelers’ devices in tandem, or asked them “to divulge their passwords, or log into their accounts, and show what’s on there,” he says. “It’s quite invasive.”
Although the Fourth Amendment to the U.S. Constitution protects U.S. citizens against “unreasonable searches and seizures” without a warrant, the country’s points of entry historically have been places where such searches are considered reasonable.
“There is no one-size-fits-all as to what should be done.” — Adam Schwartz, senior staff attorney, Electronic Frontier Foundation
International travelers have scant legal protections from customs agent searches, Jennings says, because of countries’ traditional power to control what and who enters them. Individuals’ digital data faces “three threats” at customs checkpoints, adds Adam Schwartz, a senior staff attorney specializing in civil liberties at digital-rights group the Electronic Frontier Foundation:
- searches of the local content of electronic devices, such as stored photos and documents,
- searches of cloud content accessible from accounts on those devices, such as in your Google Drive, Apple iCloud, or Dropbox accounts, and
- searches of social-media accounts, including access to the account itself—not just your public posts.
Nevertheless, people who want to keep details of their private lives secure when traveling internationally can take steps to minimize their exposure.
Step 1: Take a good look in the mirror
The first step is to consider your immigration status, your tolerance for scrutiny at the border, what you think the government of the country you’re entering wants to learn about you, and how much preparation you’re willing to undertake before flying.
“There is no one-size-fits-all as to what should be done,” Schwartz says. “There is a list of risk assessment factors, and a list of what people should do to protect themselves.”
The EFF states in its guide for carrying electronic devices through customs that all kinds of travelers should be wary of device searches, including businesspeople, doctors, lawyers, journalists, and others who have committed to professional confidentiality; private citizens whose devices store medical or legal documents; and others who simply want to maintain their digital privacy while traveling internationally.
The American Civil Liberties Union advises travelers subjected to device and account searches to write down the “name, badge number, and agency of the person who conducted the search,” and file a complaint with the agency.
Step 2: Throw chaff
You may think of yourself as uninteresting to a customs agent, but the time to realize that you might, in fact, be extremely interesting is not when you’re trying to enter a country, says Quinn Norton, a digital-security advocate and journalist who has covered the Occupy movement and the hacker group Anonymous, and was personally involved with Aaron Swartz.
Norton’s solution isn’t exactly conventional.
“Paranoia is poisonous,” she says. “Don’t try to hide your data. The more you hide your data, the more you signal your importance.”
Instead, Norton recommends “throwing chaff,” or creating multiple, inaccurate electronic records to essentially steer people away from data you want to protect.
She often enters false and “amusing” home addresses when conducting purchases online, including Chicago’s Wrigley Field. Upon returning from a work trip to Ukraine several years ago, Norton carried a laptop that was acting odd and that she was sure had been hacked. Instead of ditching it, she gave it to her teenage daughter and warned her that someone was likely spying on it. It is now the family’s default device for searching for things related to My Little Pony.
Throwing chaff to obfuscate your data and contacts is more of a mind-set than a single technique, Norton cautions.
“Get used to the idea of having multiple phones, or having phones take walks without you” by lending it to a friend to carry around for a few hours, or storing it in a cafe’s lost-and-found box while you take a walk, she advises. “When something doesn’t need your real address, move to Wrigley Field with me. You have to think, ‘How do your networks see you?’”
Step 3: Temporarily replace default accounts with travel accounts
Another strategy Norton suggests is to temporarily remove accounts from your phone and laptop that include sensitive information. Create a new account, and add to it only the bare minimum information you need to travel. Once you’ve reached your destination, you can add your default accounts.
On Wednesday, new Homeland Security Secretary John Kelly said in Congress that the United States is considering making all visitors to the country hand over their social-media account passwords, which runs against the security recommendations of Google, Facebook, Twitter, LinkedIn, Snap (formerly Snapchat), and many others.
Laurie Penny, another journalist, says her frequent reporting on feminist and cultural issues makes her digital data a “target,” even at international borders.
“Anything particularly sensitive, I keep on paper,” she says. “As a female journalist, I think a lot about kompromat,” the Russian term for compromising material that can be used to blackmail someone.
“When I’m traveling, I make sure that I have money and wallet things stashed in different places,” Norton says, in case she gets mugged. “I feel the same way about international borders and law enforcement,” so she keeps her “interesting” documents in different spots.
“Anything that’s been taken from you—assume it’s cloned. Assume it’s got a co-owner.” — Quinn Norton, digital-security advocate and journalist
For many, interesting information doesn’t necessarily indicate illegal activity, or even politically sensitive activity such as protesting in public. People suspected simply of being political activists have had their devices confiscated, searched, and sent to government facilities for “extensive forensic analysis.”
And so have government employees the CBP deems worthy of closer scrutiny.
One U.S. citizen who works for NASA’s Jet Propulsion Lab in Pasadena, Calif., publicly posted on Facebook earlier this week that CBP agents temporarily confiscated his government-issued phone. The JPL employee, Sidd Bikkannavar, added that JPL colleagues are examining the phone to see what, if anything, CBP copied, and if surveillance software was installed on the phone.
“Anything that’s been taken from you—assume it’s cloned,” Norton says. “Assume it’s got a co-owner.”
Step 4: Make backups, use encryption, and switch devices
You should regularly back up your computer and smartphone, in case they spontaneously explode or suffer from some other catastrophe that causes an irretrievable loss of data. The EFF recommends using backups also to restore data you’ve temporarily removed from a phone or laptop prior to international travel.
When you rely on cloud-based backups to restore data you’ve wiped from a phone, ensure that you restore that data over an encrypted connection such as through a virtual private network service. And be attentive to your cloud service’s own data privacy limitations, which can be affected by how long it stores your data. You can also back up your data to an external hard drive you leave in a secure spot at home.
Some people suggest traveling with “burner phones” that you can cheaply purchase and ditch. But the EFF’s Schwartz cautions that authorities can track them down rather easily, if you add a known email or social-media account to them.
If practical, it’s safer to purchase, secure, and keep more broadly connected devices in countries you frequently visit, such that you’re not crossing borders with them, Norton says. Devices you travel with would have minimal storage, accounts, and connectivity.
So how many laptops does Norton have stashed across the globe? ”That’s an interesting question,” she says, “that I neither know the answer to nor want to disclose, but most of them are crap.”
