How a hacking contest keeps you safe
VANCOUVER, B.C. —Whether your favorite browser is Apple’s Safari, Google’s Chrome, or Microsoft’s new Edge, the annual hacking contest Pwn2Own is the best place to go to watch hackers break through its defense in real time.
Pronounced “pown to own,” the contest name plays on hacker lingo at the CanSecWest convention here. To “pown” something means to take control over it.
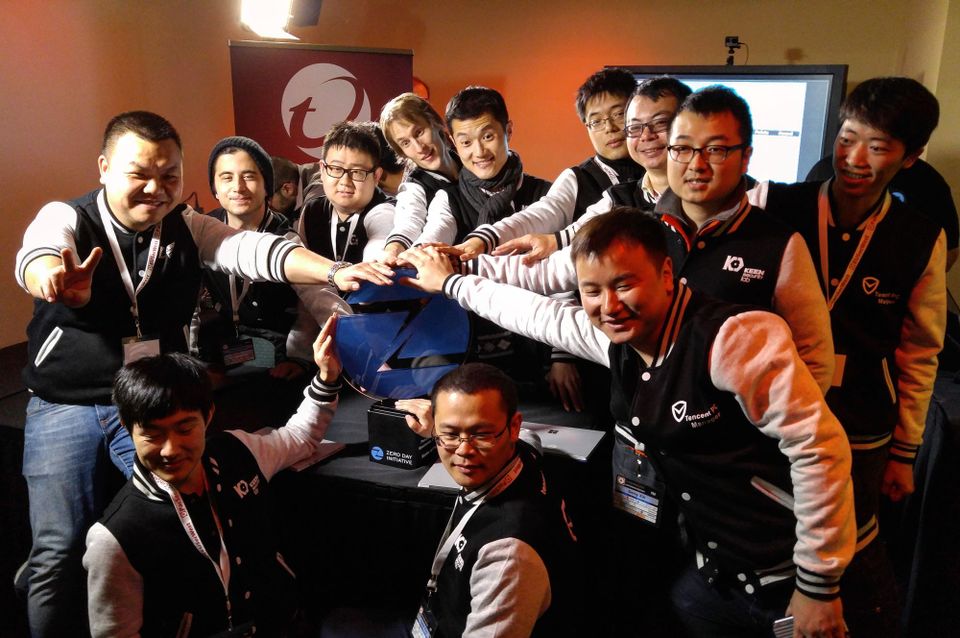
This year’s contest saw five teams take successful whacks at Safari, Edge, Chrome, and Adobe Systems’ Flash, as well as gain either system or root access to their underlying operating systems, for a total pot of $600,000. Team Sniper, made up of researchers from the Shanghai, China-based Tencent Security, took the top prize, earning a cumulative $142,500, along with purple smoking jackets emblazoned with “Master of Pwn.”
For team leader Samuel Lv, the 36-year-old director of the KeenLab at Tencent, the “2Own” aspect of the contest is about more than just earning cash prizes and counting coup against big tech companies.
“We want to prove that we are helping,” Lv says. “We help vendors fix their serious security issues.”
The point of the contest is not the prize money nor the bragging rights, echoes Christopher Budd, the threat communications manager at Pwn2Own sponsor Trend Micro. Pwn2Own gives hackers a chance to strut their stuff, but it also forces a dialogue between hackers and vendors that didn’t exist before the contest began in 2007.
The rules of the contest require hackers to disclose how they took control of their target to its maker—and give the company a chance to fix it—before publicly revealing how they pulled off the hack. Over time, the contest has gone from being a rare outpost of neutral ground between hackers and vendors to a well-established trading center.
“This is basically Grandmaster chess,” but with a twist, Budd says. Nobody’s personal security is at stake during a chess game, but the results of a hacking competition can affect every person using the hacked software. Hacks revealed at Pwn2Own could be used to steal someone’s personal or corporate information. And they could lead to headline-making tech disasters such as the Target and Sony breaches.
“Vulnerabilities are going to happen” in software, Budd says. “Cars are going to crash. What can we do to make the crash safer?”
The answer for some, even those targeted by hackers, is competitions like Pwn2Own. Tim Willis, technical program manager on Google’s Chrome Security Team, says the contest makes his team better and Google products safer to use.
“It may seem counterintuitive at first, but we want to be hacked. It helps make Chrome even more secure,” he says.
Adobe and Apple did not respond to requests for comment. Microsoft declined to comment.
Willis and other Google employees are such fans of Pwn2Own that they even assisted a hacker who failed to hack Chrome. JungHoon Lee was unable to make his exploitation of Chrome work in the allotted 15-minute window.
“We were really disappointed for him,” says Willis, so the Google team worked with Lee to successfully exploit their own browser. “We have those bugs now, and I can already see that at least one of them appears to be fixed,” he says.
What’s harder for people to see at Pwn2Own is that while a successful hack takes only seconds to infiltrate its target, planning can take days, weeks, or longer, says Charlie Miller, a former contest regular who last summer made headlines when demonstrating how he and a colleague could hack and take over a car speeding down the freeway.
“Something people may not realize is that all the hard work in participating goes in way before the contest,” Miller says. “I used to spend many weeks getting exploits ready, and then when you show up, once all the waiting is over, it only takes a few seconds to use them.”
