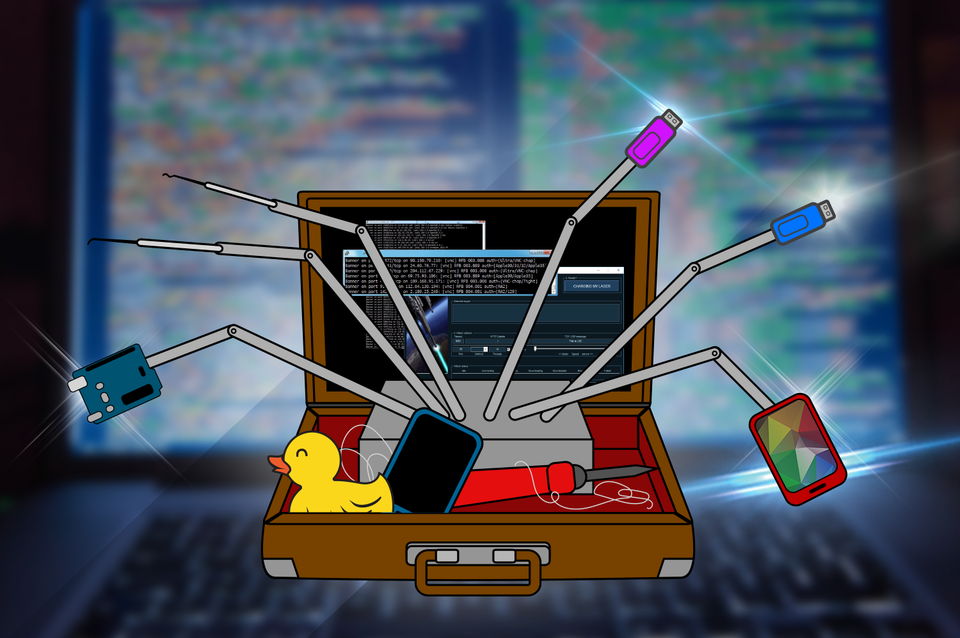
Primer: What’s in a ‘crime kit’
When a thief decides to infiltrate a bank, he needs to figure out two things: first, how he will get in, and second, what he will do when he gets in. Will he hold something for ransom? Surreptitiously steal money? Plant listening devices to glean more information?
Computer-based crime kits operate similarly. They’re automated, self-contained tools that cybercriminals of any skill level can deploy to exploit a vulnerability.
When crime kits, which often are hosted on malicious websites or compromised websites, find a vulnerable machine to exploit, they typically download on to them a payload of malware such as ransomware, botnet components, or banking trojans. For this reason, they’re largely known among security researchers as exploit kits or ransomware kits.
“There’s been a tremendous evolution with these kits,” says Brett Hansen, vice president of end-point data security and management at Dell. “This is a natural market economics thing. There’s an opportunity to transfer wealth, and the innovators—or criminals—are coming up with new techniques. What’s consistent, though, is how they operate.”
Crime kits: Born on the dark Web
Crime kits are developed by skilled cybercriminals who have identified a specific software vulnerability, developed a way to exploit it, and marketed the exploit for sale on the dark Web, Hansen says. Although some kits are available for free, others range in cost from a few hundred dollars to hundreds of thousands of dollars worth of bitcoin, adds Andra Zaharia, cybersecurity evangelist at Heimdal Security.
“These attackers want to derive as much value from their work as possible, and this allows them to enable a far larger number of people to perpetuate it,” Hansen says. “Essentially, they provide the tools to help other cybercriminals be successful with their attacks.”
That’s cause for concern, according to Hansen. Because crime kits help unskilled cybercriminals launch effective attacks, they also offer them opportunities to gain experience in cybercrime.
“This model is disturbing not only because it allows cybercriminals to scale, but because it’s great training too,” he says. “If you have thousands of sophisticated attackers, and hundreds of thousands of unskilled ones, what happens when they become more skilled? That’s what’s really worrisome.”
The motivations for developing crime kits vary, says Ted Harrington of Independent Security Evaluators. Sometimes crime kit users just want to make money, but not always. Sometimes they want to make a political statement or just cause mayhem.
Harrington suspects that some large-scale, headline-grabbing cyberattacks are “misdirection intended to obfuscate a more nefarious attack.” In other words, the perpetrator could be targeting one person—a needle in a haystack—but uses a large-scale attack to cover his tracks more easily.
All these factors contribute to why crime kits have become so prevalent, Zaharia says. The low barrier of entry makes creating, buying, and selling crime kits easy; automation enables cybercriminals to target a wide pool of users; and cryptocurrency has given them a way to surreptitiously make and receive payments.
Defending against crime kits
In 2015, a technically complex exploit kit called Angler gained notoriety for its role in spreading ransomware, as well as its links to malvertising and hacktivism campaigns. Although Angler operated like most other exploit kits, focusing on Web-based vulnerabilities in browsers and their plug-ins, it was also adept at introducing new exploits for unpatched vulnerabilities. Its effectiveness signaled inefficiencies in patching practices.
Protecting against the proliferation of crime kits requires a multipronged approach, Zaharia says. Security researchers collaborate on take-down operations that last for months and sometimes years. Working in organized groups, they target the infrastructure of cybercrime circles.
Consumers, meanwhile, can help thwart the spread of crime kits in three ways, Hansen says. The first is education—teaching the public not to click on suspicious links, for example. “Education is good, but it has its limitations. If the attackers are highly motivated, they can make it more difficult to identify a potential exploit,” he says.
Second is ensuring that your software is up-to-date—a big issue for businesses, as evidenced by the recent WannaCry ransomware. It’s a “significant effort” for companies to update hundreds of thousands of devices, he says. There are “a lot of challenges in making sure your end points are updated.”
Third is ensuring that you have antivirus and anti-malware tools installed on your devices. “There are more than 500,000 new malware variants a day, and it’s difficult for the typical tools to respond quickly enough,” Hansen says. “WannaCry was a known malware, but clearly, a lot of people weren’t protected against it. Sometimes, signature antivirus isn’t enough, which is driven in part by the growth of crime kits.”
The key to thwarting crime kits and other flavors of cyberattacks, Zaharia says, is an industry-wide shift from being reactive to proactive.
“This is something that medicine has struggled with: It’s a lot less expensive to prevent than it is to cure,” she says. “We need to shift from reacting to cybercrime to finding better ways to prevent it.”
