Ransomware is ‘blood in the water’ for hacker extortionists
After many years of data breaches and document leaks capturing the attention of the cybersecurity world, an old hacker trick is back in the spotlight—with a twist. Hackers are intent on making fast cash employing ransomware to extort money from increasingly large organizations, in addition to consumers.
People generally fall victim to ransomware by getting lured into clicking on a link or opening an attachment. Once the malware is installed, it infiltrates a target’s device, encrypts its contents, and demands payment—often via Bitcoin—before decrypting it. Over the past several months, attackers have reportedly used ransomware to extort money from several health care providers across the United States, from MedStar Health in Maryland to Methodist Hospital in Kentucky to the Hollywood Presbyterian Medical Center in California.
Although much remains unknown about the hospital attacks, including whether they are connected to each other and whether any patients were affected, we do know that ransomware attackers are demanding large sums to free corporate computers. Allen Stefanek, chief executive of Hollywood Presbyterian, said the hospital paid 40 Bitcoin (PDF), or nearly $17,000.
“Will we see a million-dollar ransom by the end of the year? Given the companies being targeted, that’s a possibility.” — Tony Robinson, computer security analyst
Like sharks detecting a big meal, ransomware extortionists “smell blood in the water,” says Tony Robinson, a computer threat intelligence analyst who this month published an in-depth history and analysis of ransomware. And they’re increasingly targeting both consumers and large organizations whose systems are vulnerable and yet whose data is valuable. “Enterprise attacks…can get thousands of dollars fairly quickly.” And that’s without even analyzing and selling the data they’ve locked up.
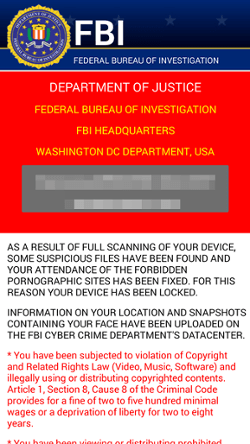
In a report it published this week, security software maker Trend Micro says ransomware authors are testing new psychological scare tactics to get victims to pay faster.
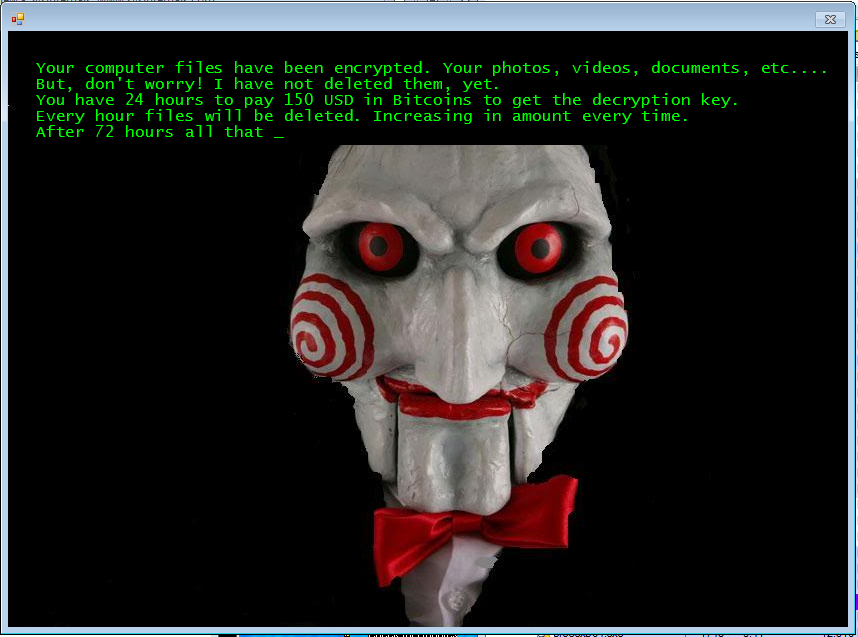
A ransomware variant called Jigsaw displays imagery of Billy the Puppet and the red analog clock from the Saw horror movies to intimidate victims. It also “toys with users by locking and deleting their files incrementally,” Trend Micro researcher Jasen Sumalapao wrote. “They encrypt a few files, and then a few more.”
Avast, a security software maker that sponsors this site, said in a report this month that its users encountered mobile ransomware at least 5 percent more in the beginning of 2016 than the previous year. Many security experts predict that in the coming months, ransomware attacks aimed at consumers’ iPhones and Android devices, as well as businesses such as hospitals that routinely gather sensitive data, will continue to proliferate.
“Will we see a million-dollar ransom by the end of the year? Given the companies being targeted, that’s a possibility,” Robinson says.
Shaky health
Attackers targeting large organizations often target out-of-date and unpatched software, says Mike Hanley, director of Duo Labs at Duo Security. Health care providers, in particular, might have vulnerable systems because of costs and complications related to upgrading them while maintaining the integrity of medical records. In a study it published yesterday, Duo Labs said its health care clients are far more exposed to attacks than its other clients.
According to the study, 3 percent of organizations running Duo security software use Windows XP, which Microsoft stopped supporting in 2014; another 76 percent are running Windows 7, which has more than 500 known vulnerabilities an IT department must address with patch installations.
“It’s a concern that [these organizations] haven’t upgraded to Windows 10 because Microsoft has made it so easy to upgrade—much easier than before,” Hanley says. Ransomware exploiting a Windows XP vulnerability recently compromised computers of Australian health care provider Melbourne Health.
Another 22 percent of Duo’s health care customers use “dangerously unsupported” older versions of Internet Explorer 8, 9, and 10. And 36 percent—three times as many as its non-health care clients—use Adobe Systems’ Flash or Oracle’s Java to run records and prescriptions apps, which are known for regularly requiring emergency security patches.
Behind the screens
Organized cybercriminal groups are driving the development of ransomware. Makers of ransomware kits, which essentially turn ransomware development into a customizable software service, often demand a cut of the profits for their efforts, Robinson says.
“A ransomware kit is much more easily available, so it’s harder to trace.” — Mike Hanley, director of Duo Labs
These groups “can develop ransomware for specific [computer] networks. They can configure how much to charge victims, how fast to encrypt their files,” Robinson says.
They can also help attackers employ “a different encryption key for every device,” says Nikolaos Chrysaidos, a mobile-malware analyst at Avast. “That makes it much harder to remove.”
For developing the ransomware, Robinson says, these groups “get a cut” of the ransoms. “It’s ransomware-as-a-service,” he says—and not one that Salesforce is likely to ever offer.
Ransomware’s next targets
Don’t expect ransomware attacks to let up, experts say. There have been repeated successful attacks on Windows, Mac OS, Linux, Android, and iOS devices, and there’s a good chance that they’re going to get harder to avoid.
Because ransomware is cross-platform, users can’t protect themselves by switching hardware or operating system. And because ransomware kits are getting easier to come by and use, attackers are getting harder to track and stop.
“If I have a unique vulnerability that I paid $10 million for,” Hanley says, referring to hackers who pay big bucks for unpatched exploits, “that can be traced back to me. A ransomware kit is much more easily available, so it’s harder to trace.”
Robinson speculates that eventually, the Internet of Things will become a ransomware target because many of those devices run embedded forms of Linux and Windows. But before you have to pay a ransom to use your microwave of the future, you’ll far more likely to get an email saying you’re past due on a bill which, in reality, is an attempt to sucker you into installing ransomware.
“The best thing you can do is trust but verify,” Robinson says. “If you owe money, call the organization, and verify it. Don’t run anything without verifying over the phone or in person.”
Coming Monday: How to avoid ransomware, and what to do if you’re infected.
