Funding fights lead to vulnerable votes

There likely isn’t a quick fix for complex U.S. election integrity challenges such as social-engineering interference on Facebook. Experts say there is a straightforward response, however, to vulnerable voting-machine software. The problem is that it involves cooperation in Congress.
When the Senate failed to move the Secure Elections Act forward in August because of White House concerns over states’ rights, coupled with funding concerns, the United States lost its best chance this year of taking steps toward patching voting machines. The most recent federal dollars devoted to improving elections came from the Help Americans Vote Act of 2002, which was itself flawed because its authors failed to predict cybersecurity standards for voting machines.
The idea of hackers infiltrating computerized voting machines at the time was “completely ridiculous,” says Margaret MacAlpine, a voting-machine security researcher and a founding partner of cybersecurity consultancy Nordic Innovation Labs.
“The cybersecurity threat was more than science fiction at that point,” she says. And even now, as knowledge that the machines are vulnerable to hackers spreads, there is still a lack of political will to allocate the funds needed to replace them and ensure that new machines are secured against attacks, she says.
Security vulnerabilities in electronic voting machines, or EVMs, have been well-documented since at least 2005, but officials often believed that the problems could be ignored because manufacturers said the machines couldn’t be connected to the Internet. That argument became invalid when manufacturers began routinely installing remote-access software on the machines. Following the 2016 election, the U.S. Department of Homeland Security declared elections to be part of the nation’s critical infrastructure.
EVMs are still in heavy use in the United States. And their security issues extend beyond software vulnerabilities: DefCon’s latest Voting Machine Hacking Village report says hackers could break even their physical locks—designed to prevent unauthorized access to the power switch, USB ports, and modem ports—in 5 seconds.
“The crux of the problem” with today’s EVM software, MacAlpine says, “is that the county officials who maintain election equipment are locked into extremely expensive service deals. But because the machine parts are so old, they can’t be maintained by the counties. It’s this horrible Catch-22.”
At stake is the ability for voters to trust that their ballots are properly counted, and for election observers to be able to verify that those ballots were cast without interference. And while counties and states nationwide have the opportunity between each election to change how they handle the country’s most sacred democratic institution, few have done much to improve electronic voting machines.
READ MORE ON ELECTION HACKING
Open source the secret sauce in secure, affordable voting tech
Experts disagree on how to secure absentee votes
Context Conversations preview: Election security
Why current funding to secure U.S. elections ‘doesn’t cut it’ (Q&A)
There’s more to election integrity than secure voting machines
Mueller’s indictment of election hackers a cybersecurity ‘wake-up call’
Post-recount, experts say electronic voting remains ‘shockingly’ vulnerable
Can your vote be hacked—after you cast it?
Instead, 24 states since 2010 have focused their efforts not on improving EVM security, but rather—based on unsubstantiated fears of widespread voter fraud—on restricting voting rights.
The National Election Defense Coalition, a nonpolitical organization of voting experts, decries EVMs, as they are currently implemented, as unsafe for election use precisely because they can be exploited for voter fraud.
“The use of computers prevents observation, and makes elections vulnerable to fraud in new and profound ways, compared to older technologies, and therefore, if computers are used, the law must require appropriate security,” the organization states on its website.
And in a survey by cybersecurity company Venafi, experts say government entities from the local to the federal level cannot be trusted to stop hacking attempts: Only 3 percent surveyed say election officials can reliably block hacking attempts, and only 2 percent surveyed say election officials can even detect hacking attempts.
Despite knowing that current EVM systems are essentially held together with chewing gum, or at least antiquated parts found on eBay, many of the nation’s leaders have thus far decided to maintain the status quo beyond Tuesday’s midterm elections and into the 2020 presidential election.
“The crux of the problem is that the county officials who maintain election equipment are locked into extremely expensive service deals. But because the machine parts are so old, they can’t be maintained by the counties. It’s this horrible Catch-22.”—Margaret MacAlpine, voting-machine security researcher, founding partner, Nordic Innovation Labs
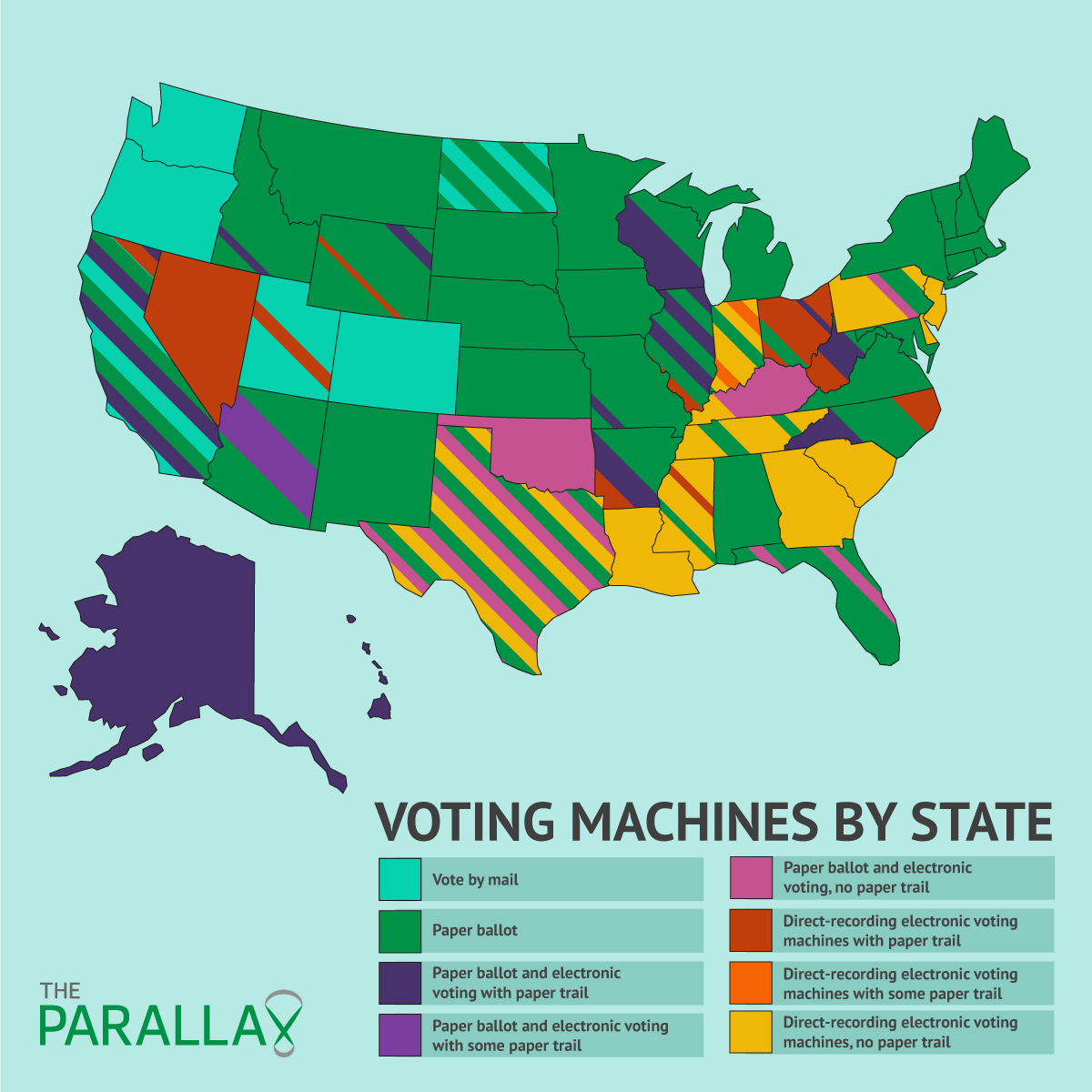
According to the election-monitoring nonprofit Verified Voting, there is no consistent voting trend across the United States.
On the state level, many election officials have chosen to revert to paper-only ballots. Three states—Washington, Oregon, and Colorado—are vote-by-mail only, a number that remains unchanged since 2014. Eighteen states plus Washington, D.C., now rely solely on paper ballots, having added only Virginia to their rolls since 2016, and Maryland and Washington, D.C., since 2014. Fifteen more states this year are using a mix of paper ballots and direct-recording (DRE) machines, with voter-verified paper audit trail (VVPAT) printers, up from 13 in 2016 and 2014.
The rest of the states offer their voters a mix of EVM and paper ballots, some with VVPATs, some not, depending on the jurisdiction. Five of those states—Delaware, Georgia, Louisiana, New Jersey, and South Carolina—use EVMs but do not create a paper audit trail in any precinct.
Paper audits for EVMs are considered essential in order to verify the voter’s intent and prevent fraud or other forms of election interference, says Marian Schneider, president of Verified Voting.
“Ninety-nine percent of votes are counted by computer,” she says, which means that, should a recount or other form of audit be required, there needs to be a paper trail to verify the audit. At the very least, she says, “Verified Voting would like to see EVM systems with paper audits.”
Every major nonpartisan election group in America appears to agree with that call, with the National Academies of Sciences, Engineering, and Medicine adding their name to a list of organizations in a September report concluding that “paper ballots form a body of evidence that is not subject to manipulation by faulty software or hardware, and that can be used to audit and verify the results of an election.”
The challenge is funding those changes, Schneider says.
“The key point is that elections have been underfunded for a long time,” she says. “We have to spend resources to make sure [voting] machines are deployed responsibly, and in a secure way.”
The National Conference of State Legislatures applauded the release of the last of the HAVA funds to the states earlier this year, but it lamented in September that the money just wasn’t enough to replace “all aging voting equipment,” let alone in time for the 2020 presidential election.
A March 2018 study co-written by the Brennan Center for Justice and Verified Voting found a wide range of cost estimates to replace paperless DREs in the states that still use them, from a low of $600,000 in Arkansas (because only a few precincts today still use them) to $79.1 million in Pennsylvania (because paperless DREs are used in every state precinct). Ultimately, the report concludes that far more than HAVA funds are needed.
To replace DRE hardware, the report estimates that the cost per precinct would fall between $6,200 and $10,000. This doesn’t include software-licensing or maintenance costs, but it’s comparable to the cost of one or two high-end consumer desktop computers.
“What we’re doing has national implications.”—Chris Jerdonek, chairman, San Francisco Elections Commission Open Source Voting System Technical Advisory Committee
Some have wondered why states don’t just use similar, commercially available off-the-shelf hardware, which would be easier and cheaper to replace than proprietary systems.
The Brennan Center report noted three thus far unsuccessful attempts to do this: in Travis County, Texas, where Austin is located, costs were prohibitive; in Los Angeles County, a $15 million contract with design company IDEO to “redesign” the voting experience appears to have stalled out; and in San Francisco, its Open Source Voting System Technical Advisory Committee has identified a complex list of publicly available components required to build a secure system—but has yet to do so.
In New Hampshire, meanwhile, an open-source configuration called the Prime III system was approved for use but got hamstrung because it can’t record the votes to a machine-readable printout.
Chris Jerdonek, a past president of the San Francisco Elections Commission who will be speaking at the Context Conversations: Election Security event, co-hosted by The Parallax on Monday evening, says his Open Source Voting System Technical Advisory Committee plans to incorporate cybersecurity standards into its specifications.
“This voting system is everything that you need to let voters vote, and to count those ballots and report on the results,” he says. “It’s made up of three components: a precinct scanner, assistance for people with disabilities, and a scanner for vote by mail.”
San Francisco, which currently spends about $2 million per year maintaining its election ballot optical scanners and other voting technology, has allocated $300,000 for development of the system.
“What we’re doing has national implications,” he says.
Ultimately, the cheapest, quickest way to secure voting systems in time for 2020 is to step away from EVMs entirely, MacAlpine says.
“Step one is to get everyone back on paper,” she says.
