Uncertain future for Wassenaar ‘cyberweapons’ agreement under Trump
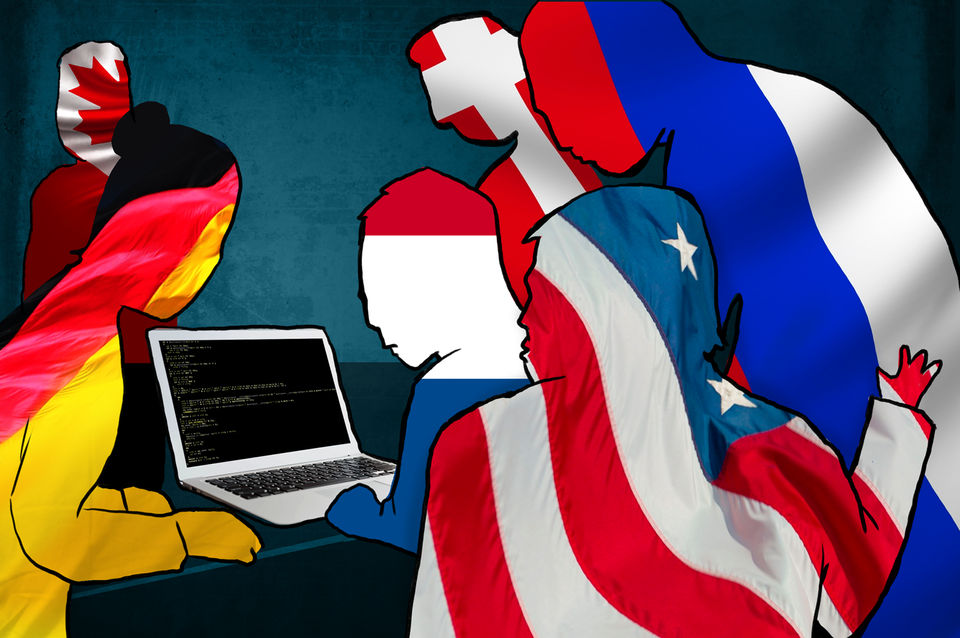
WASHINGTON, D.C.—Thanks to the unsettled status of an international weapons transfer agreement, the whims of the Trump administration over next few months could determine whether hackers and security researchers can legally share certain types of information across international borders.
The agreement, known as the Wassenaar Arrangement on Export Controls for Conventional Arms and Dual-Use Goods and Technologies, is named after the town in the Netherlands where it was first signed in the aftermath of the Cold War by most countries in Western Europe, Russia, Ukraine, Japan, and the United States. It isn’t considered a treaty because its terms are not legally binding, although its signatories abide by its recommendations.
Wassenaar regulates how weapons—including “cyberweapons”—are exchanged between the signatories. It seeks to promote “international security and stability” by ensuring transparent exchanges of “conventional” weapons such as guns, bombs, torpedoes, grenades, and mines, as well as “dual-use goods and technologies” such as nuclear centrifuges that can be used for civilian power plants or long-range weapons. And as of 2013, authors of the agreement hoped to add software and information security “items or functions.”
“The unintended consequences are the inability for defenders to exchange important information for vulnerability analysis, for malware analysis. Essentially, it would interfere with the ability of the Internet to defend itself.” — Katie Moussouris, CEO, Luta Security
At the December 2013 meeting of representatives from all the Wassenaar countries, they agreed to new regulations to control “intrusion software technology” such as malicious software, command-and-control software, and surveillance software.
Katie Moussouris, CEO of Luta Security and bug bounty expert, describes the intent of those changes as “noble.” Moussouris, who, along with Iain Mulholland, CTO of VMware, is advising the United States on Wassenaar reform, says the 2013 update proposals were supposed to “regulate the export of these things to countries that might use them to abuse human rights.”
“Really, the aim was to make it harder for organizations to sell malware, command-and-control software, [and] surveillance software to repressive regimes,” she says. But the 2013 revision proposals turned out to be broad enough to have potentially severe consequences for security researchers.
“The unintended consequences are the inability for defenders to exchange important information for vulnerability analysis, for malware analysis. Essentially, it would interfere with the ability of the Internet to defend itself,” she says, comparing the Wassenaar revision process to “writing a piece of software, and having a hacker go through and find some unintended functionality.”
Historically, the U.S. Department of Commerce has adopted the document’s language “without much debate or fanfare,” Kevin King, an export law expert, told Wired in 2015. But if the proposed updates to Wassenaar are implemented as is, security researchers could face logistical challenges in responding quickly to fast-moving threats such as botnets.

Procedures that are considered routine today, such as hiring computer security experts in a different country to examine software code for flaws, or sharing details of an exploit with a colleague or client overseas, could require an expensive export license for each instance. And even if the United States continues to hold off on adopting Wassenaar’s cybersecurity provisions, other countries could still require their researchers to acquire an export license before sharing potentially dangerous files.
Although the new Wassenaar language hasn’t been adopted, it’s already scared at least one company from sponsoring an internationally recognized hacking contest, and at least one British student from pursuing his research.
At the end of 2016, an attempt was made at a Wassenaar Plenary session to approve of revised language that would not hamstring security researchers. Clarifications to language governing command-and-control software were approved, says Moussouris, but many others were not.
That leaves Wassenaar reform up in the air but not dead—not yet, anyway. If the topic of cybersecurity control reforms makes it onto the agenda of the annual meeting of Wassenaar participants this year, technical experts like Moussouris and Mulholland could be invited to once again plead the case for revisions—possibly as early as April.
The Trump administration has been opaque about its cybersecurity policies and intentions, including whether the United States will continue to abide by or seek reform to the Wassenaar Arrangement. Trump has made it clear, though, that he’s no fan of better-known agreements between the United States and European countries, such as NATO.
Democratic Congressman Jim Langevin of Rhode Island, the co-chair of the Congressional Cybersecurity Caucus, has advocated for Wassenaar reform for several years. He tells The Parallax that he is “disappointed” that the 2016 plenary didn’t approve of the full list of recommended changes, but says he’s hopeful that the Trump administration will support the proposed updates.
“I don’t see any downside for them embracing the [proposed reform] language,” Langevin says. “There was pretty broad agreement in December to move in the direction of accepting the agreed-upon language, or something similar. I don’t think it’s going to be a high bar later in the year.”
Still, concerns that the Trump administration might decide to skip out on Wassenaar reform abound.
Arun Mohan Sukumar, the leader of the Cyber Initiative at the Observer Research Foundation in New Delhi, India, wrote in February that the apparent strengthening friendship between the United States and Russia could reduce the effectiveness of international cybersecurity agreements like Wassenaar, if other countries aren’t encouraged to participate.
“To pre-empt this development,” he wrote, other countries “are likely to build their offensive cybercapabilities, even announce their military doctrines around the exploitation of digital networks.”
There’s no backup plan, if the Trump administration decides to abandon the Wassenaar Arrangement, Langevin says, “because we believe they’re going to be on board with what we’re trying to do. This is not only bipartisan, but the government and private sector working together” he says. “There simply is no downside to [moving] this issue forward in the way we had started last year.”
Langevin had sent an open letter urging action on Wassenaar to Trump’s national security advisor, Gen. Michael Flynn, before he was forced to resign.
The lengthy negotiation and reform process, which has been under way for several years, does have one upside, Moussouris says: Hackers and government leaders are learning to interact better, and avoid regulation language, as included in the Computer Fraud and Abuse Act and the Digital Millennium Copyright Act, that could prevent security researchers from doing their jobs.
“We’re going through some growing pains here, but we’re learning how to meld together these two vital areas that are shaping our worlds: technology itself, and the policies, regulations, and laws to govern it,” she says. “Imagine if we had had this process back when the original CFAA and DMCA were drafted.
