Behind hackers’ love affair with unofficial conference badges

LAS VEGAS—John Adams looked more than a little exhausted on Friday evening in San Francisco, as he stared down three large cardboard boxes filled with touch screens, electronics parts, and circuit boards he designed with his hacking partners, Egan Hirvela, Bill Paul, and Matthew Harris.
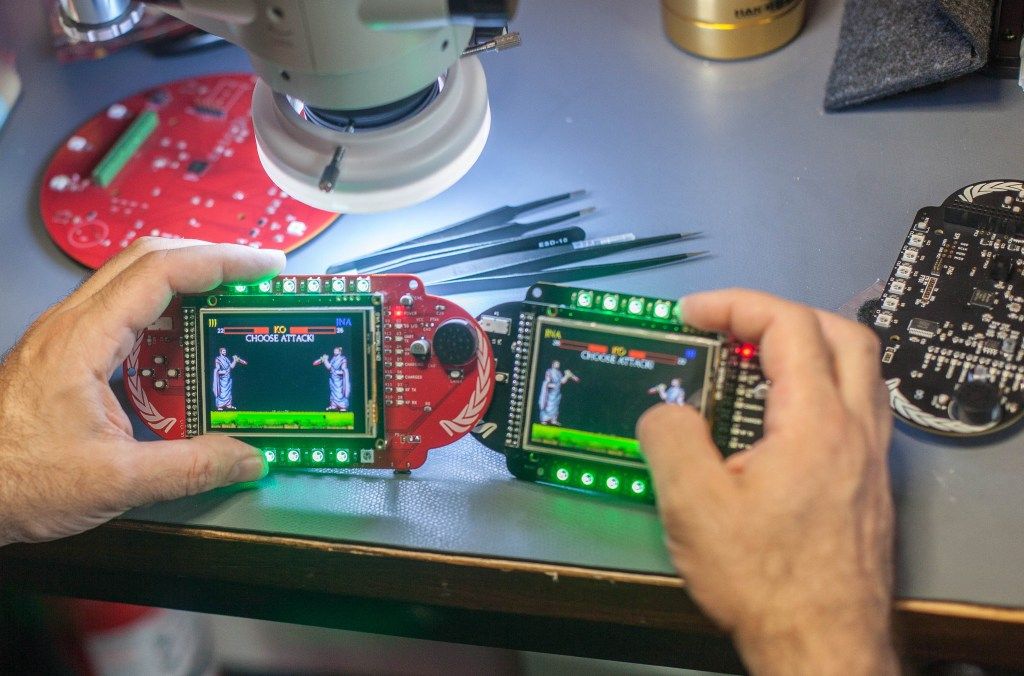
What might resemble to some a PlayStation Vita console lacking its shiny plastic case is actually a year’s worth of work on the Ides of DefCon, a Roman gladiator-theme fighting game and hackable electronic-badge project for attendees of the 25th annual DefCon, the largest hacker conference in North America, to be held at Caesar’s Palace here this week.
“I expected a 10 percent failure rate,” Adams says, wearily eyeing the boxes. More than a third of the 225 badges his team had painstakingly designed and written original software for had arrived from the Texas manufacturer in varying states of dysfunction, owing in no small part to problematic component choices Adams and his team had made.
After sending out 94 functioning badges to the Kickstarter supporters who had contributed more than $23,300 to the project, Adams decided to try to fix as many of the broken badges as possible before loading up a rental van with the boxes and heading southeast through the desert to DefCon. In just a few days, they cobbled together an electronics lab complete with a high-power microscope and a hot-air station, and worked furiously.
“I’ve spent a year getting into the electronics rathole,” says Adams, who led Twitter’s security team when it was a fledgling service. “This is a project that went way too far.”
Yet as he pulled into Vegas on Monday night with little sleep, he noted that his team’s valiant efforts had paid off: They brought with them 92 additional functioning badges.
In its final form, the Ides of DefCon badges, whose development was partially backed by Avast, sponsor of The Parallax, feature multicolored LEDs, digital-audio playback, 4GB microSD cards, 915MHz radios, tilt sensors, and color touch screens. Each set of components is powered by a rechargeable battery and, through a customized version of open-source development environment ChibiOS, is hackable.
Ides of DefCon badge holders can create their own gladiator character, then battle other badge holders on the conference floor. Win enough battles, and they can climb up 10 increasingly difficult levels. As they play, they’ll encounter a bevy of Easter eggs and mental puzzles. They might even get Rickrolled.
This year, as in the past, there are at least 10 unofficial badge projects like Ides of DefCon. One badge doubles as a quadcopter. Another, inspired by Neal Stephenson’s science fiction novel The Diamond Age, takes the form of a dragonfly. A classic arcade game badge is shaped like a Hunter S. Thompson-ified Bender from the Futurama cartoon, and another is inspired by Mr. Robot. Still others were built for specific social groups or other conferences here this week, including QueerCon.
Five years ago, the Ninja hacking group’s entry badge for its annual party was the NinjaPhone: a customized version of Android running on an HTC phone on its own cellular network, Ninja Tel.
Brandon Creighton, who worked on the Ninja Tel project, says that while device-manufacturing costs have fallen since then, badge projects are still expensive and therefore attract designers who have time and money—or the will to raise it.
“You’re not going to understand IoT device security just by breaking the software.”—John Adams, lead developer, Ides of DefCon conference badge
“It’s so great to see so many people get involved,” he says, “But it’s still high-risk. All your displays are on one chip, and if that chip fails, you’re out of luck.”
DefCon’s official admissions badge—which each attendee receives, risk-free—includes a hackable puzzle, and there are plenty of cheap Internet of Things devices to hack at the conference and elsewhere. So why are hackers bothering to play around with unofficial badges, let alone spending a year to develop them?
Unaffiliated, limited-edition (and thus exclusive) badges are utilitarian status symbols for the DefCon cognoscenti. They also entice hackers to immerse themselves in learning skills alongside engaged community members, without the legal (or physical) risks associated with hacking an Internet-connected car or medical device.
“Connected devices in the aggregate are easier to exploit than phones or computers,” says Ted Harrington of Independent Security Evaluators, a computer security company that specializes in device testing and that runs the IoT Hacking village at DefCon, which this year will feature products from Apple, Amazon.com, Google, Fitbit, as well as an Internet-connected tank from NXT Robotics. And conference badges, he argues, provide an effective and safe introduction to IoT hacking.
“Hacking a badge isn’t any different than hacking any other devices,” Harrington says. “That’s what hacking is—it’s solving the puzzle.”
“You’re not going to understand IoT device security just by breaking the software,” Adams adds. Sometimes, “you have to use hardware to attack hardware. You can’t plug in a keyboard or mouse.”
Ben Hibben, a Web developer for General Electric Appliances who designed this year’s Mr. Blinky Bling badges to scan for Wi-Fi networks, says the communities created by the badges are just as important to hackers as the skills they learn by hacking them.
“Badges have a community,” says Hibben, an active member and former board member at the LVL1 Hacker Space in Louisville, Ky. “The people who buy them are going to talk to each other about what they’ve done and how they’ve done it.”
