Triaging modern medicine’s cybersecurity issues
Hackers often talk about practicing good “cybersecurity hygiene”: making sure that basic standards, such as using unique passwords for each log-in, are met. And they say it’s high time for the entire health care ecosystem, from clinicians to hospital systems to insurers, to scrub in and get to work on better protecting medical data and devices.
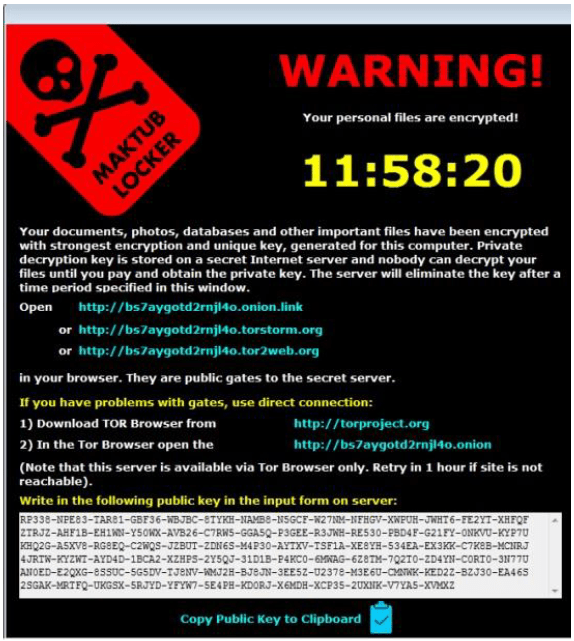
Cybercriminals today are intent on holding hospital databases hostage with ransomware, or stealing patient data for resale on the Dark Web. That’s because medical data can include financial information, home and work addresses, emails, Social Security or other national identification numbers, insurance information, medical diagnoses, and even personal images.
This breadth of information can be much more valuable on the black market—sometimes up to $30 per record—than the typical consumer financial profile, which sells for $10 to $12. (Andrei Barysevich, the director of advanced data collection at cybersecurity research company Recorded Future, however, says most medical records are sold in bunches of 1,000 to 200,000 for a flat fee of about $1,000, which could bring down the cost of a single record to $1 or less.)
In their pursuit of patient data, cybercriminals often reach for the lowest-hanging bunches of fruit, which often are the least secured legacy Windows computers, as well as Internet-connected devices collectively known as the Internet of Things.
For basic evidence of this trend, look no further than Sutter Health, a Northern California-based organization of 24 hospitals, 36 surgery centers, and more than 5,500 doctors.
Jacki Monson, Sutter Health’s chief privacy and information security officer, tells The Parallax that as the number of connected devices on the Sutter Health network exceeded 91,000 this past year, the number of cyberattacks against the organization more than tripled.
READ MORE FROM ‘NO PANACEA FOR MEDICAL CYBERSECURITY’
Why health care cybersecurity is in ‘critical condition’
How to recover from a health care data breach
Ransomware attacks against hospitals: A timeline
How weak IoT gadgets can sicken a hospital’s network
Opinion: Who foots the bill for medical IoT security?
To prevent EHR breaches, stop using them (Q&A)
“We’ve seen, on average per month, 38 trillion attempted attacks this year,” she said during a phone conversation at the end of August. “Last year at this time, that was 10 trillion per month.”
Monson declined to state how many of those attacks were successful, but she did say other health care organizations of similar sizes are seeing the same level of attempts to get into their computer systems. Our timeline of ransomware attacks against hospitals and patient care clinics since 2016 highlights more than 30 successful and publicly acknowledged attacks, many affecting multiple institutions. (Sources tell The Parallax that around the world, there likely have been many more.)
Although technology has become the lifeblood of the health care industry, hospitals and patient care clinics are often ill-equipped to confront a Hydra-headed monstrosity: Attacks against health care organizations are skyrocketing. Countless flaws in medical devices are going unpatched. Regulations often stymie efforts to respond to patient and doctor needs. Thin financial margins make it difficult to hire and retain talented cybersecurity professionals. And doctors don’t necessarily see cybersecurity vulnerabilities as a threat to patient safety.
READ MORE ON MEDICAL SECURITY
Biohacker’s latest answer to health care hurdles: Homebrew meds
On doctors’ orders, Israel plans a health care CERT
WannaCry vs. the ER doc: On the front lines of a ransomware outbreak
Yes, your life-saving medical devices can be hacked
Critical systems at heart of WannaCry’s impact
Time for a Department of the Internet of Things?
Hackers call for federal funding, software security regulations
The edge of heartbreak: Researcher hacks her own pacemaker
A 2017 study by the American Medical Association and Accenture found that while more than 83 percent of doctors say they have experienced some form of cyberattack, only half of those surveyed are worried about future attacks. And a March 2018 report by medical cybersecurity company Merlin International found that 65 percent of health care executives lack a strategy for securing medical devices on their networks.
Nor has there been an industrywide focus on addressing technological vulnerabilities in health care practices. Despite broad knowledge of the scope of breaches, enabled by mandated reporting requirements in the Health Information Technology for Economic and Clinical Health Act and the Health Insurance Portability and Accountability Act, a June 2018 report in the Journal of the American Medical Informatics Association Open lamented a lack of a “formal analysis” of data breaches related to electronic medical records and hacks.
“We’ve seen, on average per month, 38 trillion attempted attacks this year.”—Jacki Monson, chief privacy and information security officer, Sutter Health
Many of the breaches are preventable, researchers say. The McAfee Labs Threat Report from March 2018, which found that cybersecurity attacks against the health care industry had risen 211 percent over 2016, stated that many of the successful hacks could have been stopped by implementing “security best practices,” including changing default passwords and applying software patches in a timely manner.
The problem with ‘just patching’
A common refrain in cybersecurity is to “just patch” vulnerabilities by installing available security updates for devices. WannaCry and NotPetya, which decimated systems of medical organizations and partner companies around the globe, both exploited a critical vulnerability for which Microsoft had delivered a patch just weeks beforehand.
Patches, of course, aren’t always simple—or even free—to install.
Software updates for patient monitors or wheelchairs might not be such a big deal, but for devices considered critical to patient care, including CT and MRI scanners, health care organizations must choose between purchasing a newer device for hundreds of thousands or even millions of dollars, or forking over smaller sums of money to securely maintain existing systems.
In an announcement revealing new maintenance costs, Microsoft last week said it will begin charging organizations and individuals to continue to use devices running its legacy Windows 7, which nearly 40 percent of Windows computers still use.
“There’s no forensics being done on these devices.”—Dr. Christian Dameff, emergency medicine and critical-care specialist, University of California San Diego Medical Center
A Microsoft representative said in an email to The Parallax that the tech giant is “committed to helping” its customers but won’t waive Windows 7 charges for medical organizations.
“We are working with our customers and partners to provide Windows 7 Extended Security Updates in a variety of scenarios, including embedded and IoT versions of Windows 7, which would likely include medical devices,” according to the statement. “We are helping customers to ensure they have the upgrade path in place that gives them the flexibility and security they need while they make the move to Windows 10.”
Installing patches for medical devices implanted inside the body—including deep-brain neuro-stimulators, cochlear implants, gastric stimulators, insulin pumps, foot-drop stimulators, or pacemakers—is even more complicated and risky. If a patch is faulty, and a device malfunctions, a patient can get seriously harmed or even die.
Medicine is facing too perfect a storm of complications and competing interests for compromised devices to never hurt patients, says Dr. Christian Dameff, an emergency medicine and critical-care specialist, as well as clinical informatics researcher, at the University of California San Diego Medical Center.
When medical devices such as heart monitors or dialysis machines malfunction, they are almost always dealt with in one of two ways, he says: They have their firmware wiped and are put back into use; or they have their hard drives pulled and are sent back to the manufacturer for repairs.

A Trend Micro report from April 2018 about challenges in securing hospital systems further reveals that many critical systems are exposed on Shodan, a search engine of accessible Internet-connected devices.
“Exposed medical systems potentially jeopardize critical data such as patients’ personally identifiable information (PII) and medical records,” the researchers wrote. “Perpetrators can, with additional effort, disrupt hospital, clinic, and pharmacy operations by corrupting sensitive data, issuing incorrect device commands, infecting systems with ransomware, and so on.”
“There’s no forensics being done on these devices,” Dameff says. A hard drive may contain cryptomining malware, which can slow down or cause other malfunctions on devices. And restoring a device’s firmware to factory settings may not remove any potential malware infestation.
Compounding the various technical complications of patching is a more cultural problem, security researchers say: simply not taking security seriously.
When researchers reported to Internet-connected medical-device manufacturer Medtronic a pacemaker vulnerability, for example, the company took 10 months to determine that, from its point of view, the risk to patients was “acceptable.” Billy Rios, who along with Jonathan Butts conducted the research project, says the vulnerability remains exposed more than 570 days after first reported.
Medtronic spokesperson Erika Winkels wrote in an email that the company is “in regular communication” with regulators and the researcher community, and continues to “address vulnerabilities” that it knows about. “We are reviewing in detail the issues highlighted at Black Hat, and we don’t have anything further to share at this time.”
Federal regulators seem to agree with Dameff, Rios, and other medically minded cybersecurity researchers that medical-device manufacturers need to take reported threats more seriously. The U.S. Food and Drug Administration revealed plans in April to create a “go team” to address medical-device cybersecurity incidents. FDA director Dr. Scott Gottlieb supports taking device security seriously. And at least one of his colleagues has criticized device makers for not acting in good faith.

At the Security BSides Las Vegas hacker conference in August, Dr. Suzanne Schwartz, the FDA’s associate director of science and strategic partnerships, reiterated to The Parallax what she said last year, regarding medical-device manufacturers and cybersecurity: “The stakes are high here.”
Dameff argues that the only way to get all of the stakeholders—including doctors, hospitals, and device manufacturers—to take action is to normalize vulnerability-reporting practices. And to do that will require better cybersecurity education, says Josh Corman, chief security officer of software maker PTC, who has been working on bridging stakeholders in medicine with cybersecurity experts since he co-founded I am the Cavalry in 2013.
“The answer to bad patching isn’t to stop patching—it’s better patching,” he says.
Medicine as critical infrastructure
The complexities involved in securing connected medical devices are only part of the larger challenge in securing medical infrastructure, which many countries consider part of their public-health critical infrastructure. And in today’s connected world, this infrastructure goes far beyond hospital organizations and disease prevention systems.
Pharmaceutical manufacturers like Merck, part of the chemical sector of critical infrastructure, for example, are also part of the public-health sector. So is Nuance, a major provider of medical-transcription services. Many hospitals around the world rely on Nuance to encrypt and provide on-the-fly transcription of doctor’s notes, prescriptions, and referrals.
“Delayed and degraded patient care can hurt patient outcomes.”—Josh Corman, chief security officer, PTC, and co-founder, I am the Cavalry
NotPetya cost Merck more than half a billion dollars. It also set Nuance back at least $92 million, as organizations like Sutter Health hired dozens of temporary staffers for medical transcription, The Parallax has learned.
Only the largest industry players seem positioned to absorb such costs, which are clearly separate from the costs to patients, Corman says.
“Handwritten notes [taken during Nuance’s transcription outage] delayed patient care. Multiply that by the number of patients doctors saw, the number of days Nuance was down, and you get significant delays,” he says. More simply put: “Delayed and degraded patient care can hurt patient outcomes.”
Corman’s assertion jibes with findings in an April 2017 New England Journal of Medicine study that looked at how marathon-related road closures impact patient care. The study’s authors concluded that on marathon days, on average, ambulances take 4.4 minutes longer to get patients to area hospitals before noon. And patients admitted to hospitals on marathon days are 13.3 percent more likely to die within 30 days of hospitalization than patients hospitalized on non-marathon days.
If “delayed” or “degraded” care due to marathons hurts patient outcomes, wouldn’t delays and degradations due to cyberattacks also hurt patients?
Sacramento area obstetrician Dr. Erin Hefley relishes the way medical technology has allowed her to stay in touch with her patients. Hefley, who has presented at the hacker conference DefCon, says advanced systems like remote fetal monitors, and standardized technology like electronic medical records, have made it easier for her to help patients.
“All day long, I can communicate with my patients,” she says.
She’s worried, however, about a lack of consistent security protocols and policies. While doctors are required to use a secure VPN tunnel to remotely access patient records, patients themselves are required only to have a simple username and password—two-factor authentication would be more secure, she says. She also worries about threats out of the control of doctors or patients, such as the NotPetya attack or the more recent SamSam ransomware attack, which took down EMR provider Allscripts for eight days and affected 180,000 doctors.
“Any time the EMR goes down, it affects patient care. If you can’t look up somebody’s medical history, their prior labs, their contraindication medicine, I could potentially intervene in a way that causes more harm than good.”—Dr. Erin Hefley, obstetrician
While impacted by ransomware attacks, Hefley and fellow clinicians scrambled to get accurate medical histories for their patients.
“Any time the EMR goes down, it affects patient care. If you can’t look up somebody’s medical history, their prior labs, their contraindication medicine, I could potentially intervene in a way that causes more harm than good,” Hefley says. “It’s going to affect your ability to deliver safe and timely care.”
No panacea for what ails modern medicine
Securing today’s health care systems, numerous medical and cybersecurity experts say, will require more publicly discussing and addressing their cybersecurity weaknesses—without scaring patients away from advanced technology. The fact that a cardiac patient’s Wi-Fi-connected pacemaker can be hacked, they argue, doesn’t mean that it actually will be hacked. And even if it is hacked, it may still function well enough to keep the patient alive.
Ultimately, Dameff says, it’s up to doctors and nurses to “normalize” talking about cybersecurity problems with their patients. And that will require strategizing. According to a May 2018 study in the Journal of Medical Internet Research, health care organizations intent on improving their cybersecurity must focus on strategy and implementation, instead of “blindly” throwing more resources at the problem.
The cybersecurity challenges health care is facing are hardly new, of course, and in the rush to adopt new technology, health care clinician and informatics expert Nina Alli worries that the very idea of caring for the patient has been “lost.”
“The medical side is not in sync with the technology side. That’s a problem, when there’s a patient that needs to be cared for,” she says. “Hope is not a security strategy.”
Update, September 18 at 4 p.m. PST: Added a comment from Medtronic.
