Can we abandon email for secure messaging? Not so fast
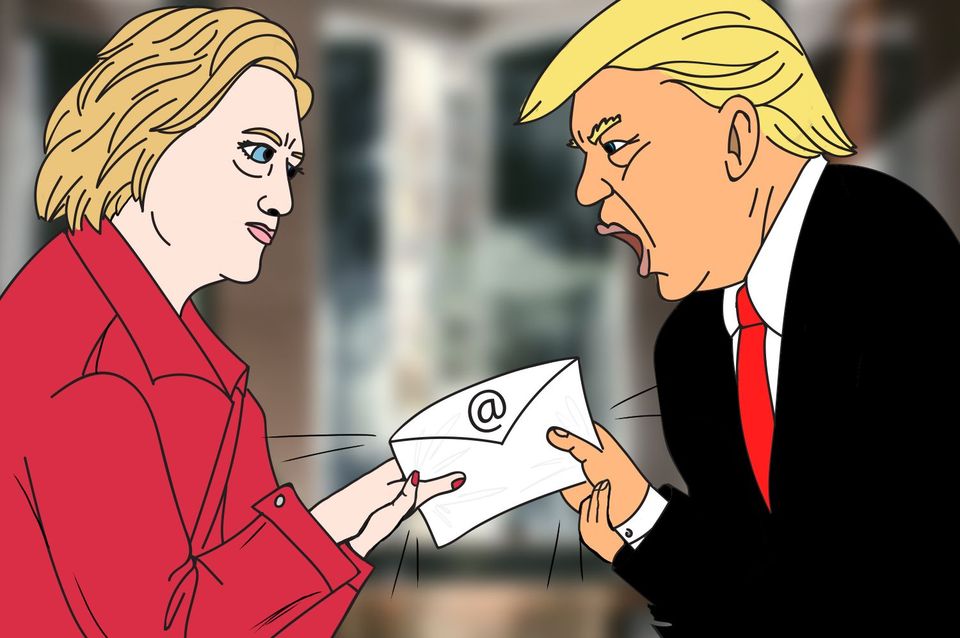
In 1986, decades before the email leak scandals surrounding Hillary Clinton’s presidential campaign and the Democratic National Committee spent weeks splashed across news headlines, Ollie North and John Poindexter scrambled to wipe messages from their White House computers and got caught up in a well-documented affair known as Iran-Contra.
If email leaks have been driving government and corporate scandals for more than 30 years, why are organizations still using email to send sensitive messages and documents?
Email can be protected from casual snooping using cryptographic computer code. The most commonly used technology to encrypt email is Pretty Good Privacy, or PGP, a cryptographic key exchange system. But according to PGP’s inventor, Phil Zimmermann, there are better ways today to securely send sensitive data.
“When I did PGP 25 years ago, I designed it to deal with the threat models that existed at that time, and a bit beyond that time, but not 25 years in the future. [The year] 1991 was a time when very few people had email,” he told The Parallax. “If you’re very careful about using PGP, you can use email for secure communications. But I qualify that heavily because the threat model has changed so much in the past 25 years.”
When Zimmermann initially worked on PGP and securing email, he says the original security reason to encrypt email was to stop “man in the middle” attacks, through which someone could intercept and read a message. PGP’s key exchange requires the email’s sender and recipient to verify each other’s identities.
“Anything you write down and put on digital media, you might as well put on a billboard in front of your company.” — Paul Vixie, Internet pioneer
Modern email faces newer security demands that PGP can’t fulfill. Zimmermann says these include incorporating forward secrecy (which prevents a hack of current encryption keys from exposing emails protected by previously used keys), and reducing the amount of metadata broadcast in each email.
Since the early 1990s, as computer security threats have evolved—and as email security has essentially stood still—consumers and organizations have continued to insist on using and storing sensitive information in email. And as they have become accustomed to having years or even decades of archived email to peruse at their leisure, hackers have been able to illicitly access and publicly publish (often at sites such as WikiLeaks) these stored messages.
READ MORE ON EMAIL AND SECURE MESSAGING
Why weakening encryption can hurt you
How to avoid phishing scams
Timeline: Encryption throughout human history
Parallax Primer: Why people are flocking to messaging app Signal
What you need to know about WhatsApp’s new terms of service
How political campaigns target you via email
Such message leaks can be catastrophic. Email conversations that have moved from private to public have derailed the careers of politicians, exposed Hollywood antipiracy schemes and executive biases, and revealed corporate tax dodging.
“Anything you write down and put on digital media, you might as well put on a billboard in front of your company,” says Internet pioneer Paul Vixie, now the CEO of Farsight Security. “Don’t put anything in an email that you don’t want on the front page of The New York Times tomorrow.”
Email, nevertheless, remains the most popular electronic medium with which to communicate by several orders of magnitude, and it’s not going away anytime soon.
In its annual report, market research firm Radicati estimated that by the end of 2016, more than 2.67 billion people used email. With a 3 percent annual growth, that tally will surpass half of the world’s population by 2020. Likewise, the firm predicts that the daily total of email messages sent in 2016, 215.3 billion, will grow by 4.6 percent per year to hit 257.7 billion emails sent per day in 2020.
“Confidential file sharing over email is a mistake.” — Galina Datskovsky, CE, Vaporstream
Largely because the process of using PGP with email is complicated enough to vex even security professionals, many security experts are advising consumers and businesses to stop using email for sensitive communications. Vixie, among them, says there is “no way” to get PGP into wide use because using it requires a “Rube Goldberg contraption of a workflow.”
“It’s too hard to get people to remember their ATM card PIN, let alone email PGP keys,” he says. Privacy-minded individuals, he says, are turning in large numbers to messaging apps incorporating end-to-end encryption such as Signal, WhatsApp, and Wickr to electronically send highly sensitive information.
Those apps, Vixie acknowledges, have a steep hike ahead of them. While some encrypted services—most notably WhatsApp, which, as the single-most used end-to-end encrypted messaging app by far, supports more than 1.2 billion users, sending 60 billion messages a day—have had some “moderate business success,” he says convincing billions of others to make the switch is going to be tough, largely because of the walled-garden approach they employ that is at the heart of their secure communications.
Apps requiring both senders and recipients to use them, much like PGP does but seamlessly, “have made the ability to communicate securely much more within reach,” says encryption expert Galina Datskovsky, CEO of Vaporstream, which makes a communication app for businesses that sends and self-deletes encrypted messages. “Confidential file sharing over email is a mistake.”
“Just because you have an encrypted protocol, particularly one that’s automated, doesn’t necessarily mean it’s been implemented with the highest levels of security possible.” — Ladar Levison, founder, Lavabit
But even though Signal and WhatsApp use the same encryption protocol, you can’t send a message from Signal to WhatsApp, or vice versa.
That walled-garden approach makes it easier to confirm the cryptographic key exchange that has been tripping up email users for decades. “You can’t offer security, if you don’t control both ends,” Datskovsky says. But it also serves as a literal barrier to broad adoption, Vixie says.
“All of these ephemeral communications people are creating are closed communities. For most of us, we have to join more than one to reach everybody we want to reach. You’re just adding a few secure paths to the insecure ones that already exist,” he says. “That just tells us that some people are going to get a little bit safer when talking to their friends. But I don’t think we’re moving the needle until the whole world is on something as ubiquitous as email.”
Ladar Levison, who ran the encrypted-email provider Lavabit, best known for being used by Edward Snowden before he shut it down over FBI access demands, is one Internet entrepreneur who thinks that there’s still hope for secure email.
“Just because you have an encrypted protocol, particularly one that’s automated, doesn’t necessarily mean it’s been implemented with the highest levels of security possible,” Levison says.
Levison resurrected Lavabit in January as an end-to-end encrypted email provider that allows users to choose different levels of security without having to juggle PGP keys.
“Traditional email is ill-suited for handling secrets,” he says, and app makers could, without user knowledge, spy on their customers. “I’ve created a framework that allows you to exert the level of control that you feel is appropriate, given your threat model,” he adds. “The goal is, make the schema ubiquitous so each side of the conversation can choose their level of security themselves.”
